What is Tailscale?
Last validated:
Tailscale is a Zero Trust identity-based connectivity platform that replaces your legacy VPN, SASE, and PAM and connects remote teams, multi-cloud environments, CI/CD pipelines, Edge & IoT devices, and AI workloads.
Out-of-the-box, Tailscale solves many networking headaches. It has a customizable configuration to meet the demands of managing a distributed workforce. Tailscale helps provision for internal self-hosted and external third-party applications. It scales for growth as your requirements change.
Tailscale is an ideal solution for DevOps, IT, and Security teams.
Technical details
Tailscale is a secure networking solution that streamlines connecting devices and services securely across different networks. It enables encrypted point-to-point connections using the open source WireGuard protocol, which means only devices on your private network can communicate with each other.
Tailscale creates a peer-to-peer mesh network (known as a tailnet). However, you can still use Tailscale like a traditional VPN by routing all traffic through an exit node.
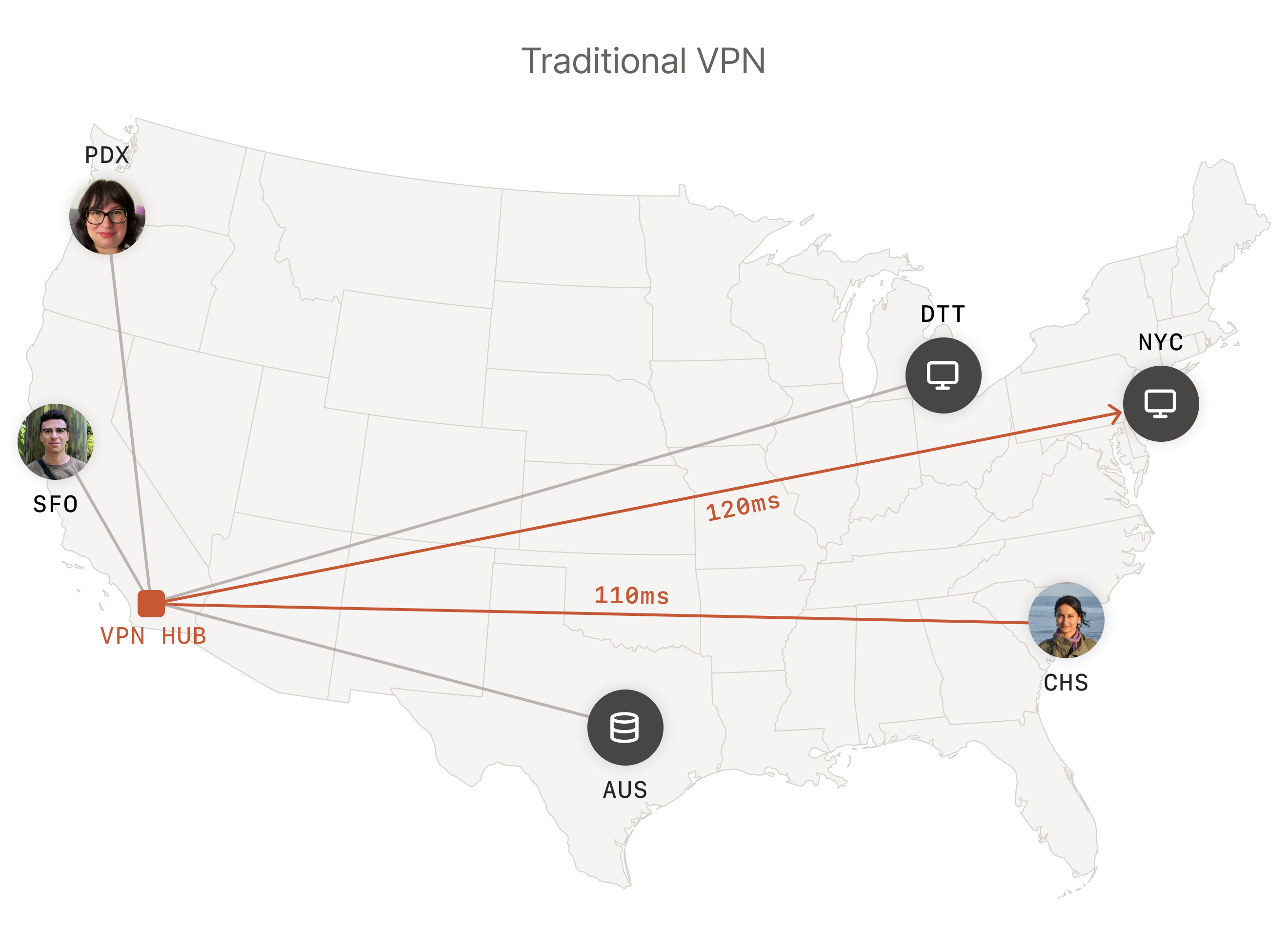
Figure 1(a). The central gateway may or may not be close to users, thus resulting in higher latency. Because traffic is centralized, it can also act as a bottleneck, slowing down connections further.
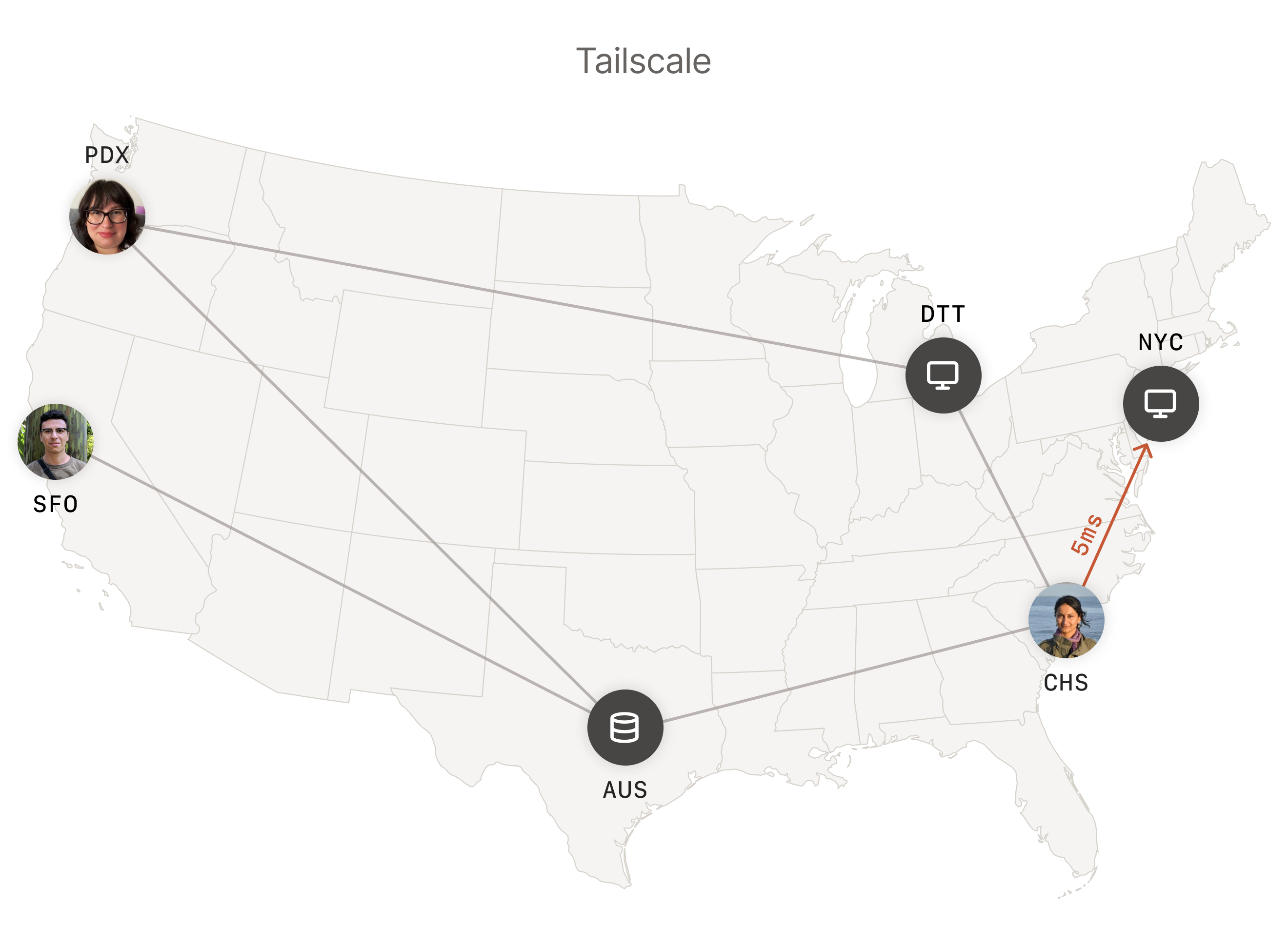
Figure 1(b). With Tailscale, each device is connected to the other directly, resulting in lower latency.
The Tailscale approach avoids centralization where possible, resulting in both higher throughput and lower latency as network traffic can flow directly between devices. Additionally, decentralization improves stability and reliability by reducing single points of failure.
For more information, refer to how Tailscale works.
Benefits
Some key advantages of Tailscale include secure and private connections between devices, a flexible network topology, and a streamlined setup. Tailscale is also cross-platform, infrastructure agnostic, and highly configurable. It supports the features you need and the integrations that you currently use.
For more information, refer to why Tailscale is right for you.
Streamlined setup
You can deploy a tailnet in minutes without requiring extensive configuration, server setup, and networking expertise. After you create an account, authenticating two or more devices automatically creates a tailnet with a sensible set of default access policies.
Connections between tailnet devices work seamlessly across firewalls and Network Address Translation (NAT) without requiring port forwarding or complex firewall rules. This "zero config" approach dramatically reduces the technical barriers to implementing secure networking, making it accessible to technical and non-technical users.
Security and privacy
The Tailscale security model is built on modern, proven technologies and best practices such as end-to-end encryption and a zero-trust architecture. At its core, Tailscale uses WireGuard, a state-of-the-art VPN protocol known for its security and performance. This foundation is enhanced by Tailscale's commitment to compliance, security policies, and security features such as access control policies and Tailnet Lock.
Scalability and adaptability
Tailscale's flexible architecture is designed to grow seamlessly with your organization's needs. Whether you're scaling from a small team to a large enterprise or expanding across multiple geographic locations, Tailscale maintains its performance and security characteristics at scale. The distributed nature of its architecture means that adding new devices or users doesn't create bottlenecks that typically plague traditional VPN solutions.
Use cases
With its low barrier to getting started, versatility, and powerful capabilities, Tailscale seamlessly scales from personal use to enterprise deployments. Developers can use it to share work-in-progress features with their team, homelab enthusiasts can use it to access their media servers remotely, and businesses can use it to secure their distributed workforce, all without the hassle and overhead of traditional infrastructure setup and maintenance.
- Business Virtual Private Network (VPN): Replace your legacy VPN and enable secure remote access to infrastructure.
- Privileged Access Management (PAM): Enable Zero Trust with just-in-time access and robust recording.
- Workload connectivity: Connect pipelines, apps, and Kubernetes workloads.
- Continuous Integration and Continuous Delivery (or Deployment) (CI/CD): Granular secure access to every runner and workload.
- Edge and Internet of Things (IoT): Access, manage, and monitor thousands of devices.
- Securing Artificial Intelligence (AI): Unified AI governance for AI agents and users.
For more information, refer to Tailscale Testimonials and Tailscale Use Cases!
Get started
Getting started is as simple as creating an account, installing the Tailscale client, and logging into two or more devices. Visit the quickstart guide to learn more.
To stay in touch, sign up for our newsletter.