Understanding mesh network topology (mesh VPNs)
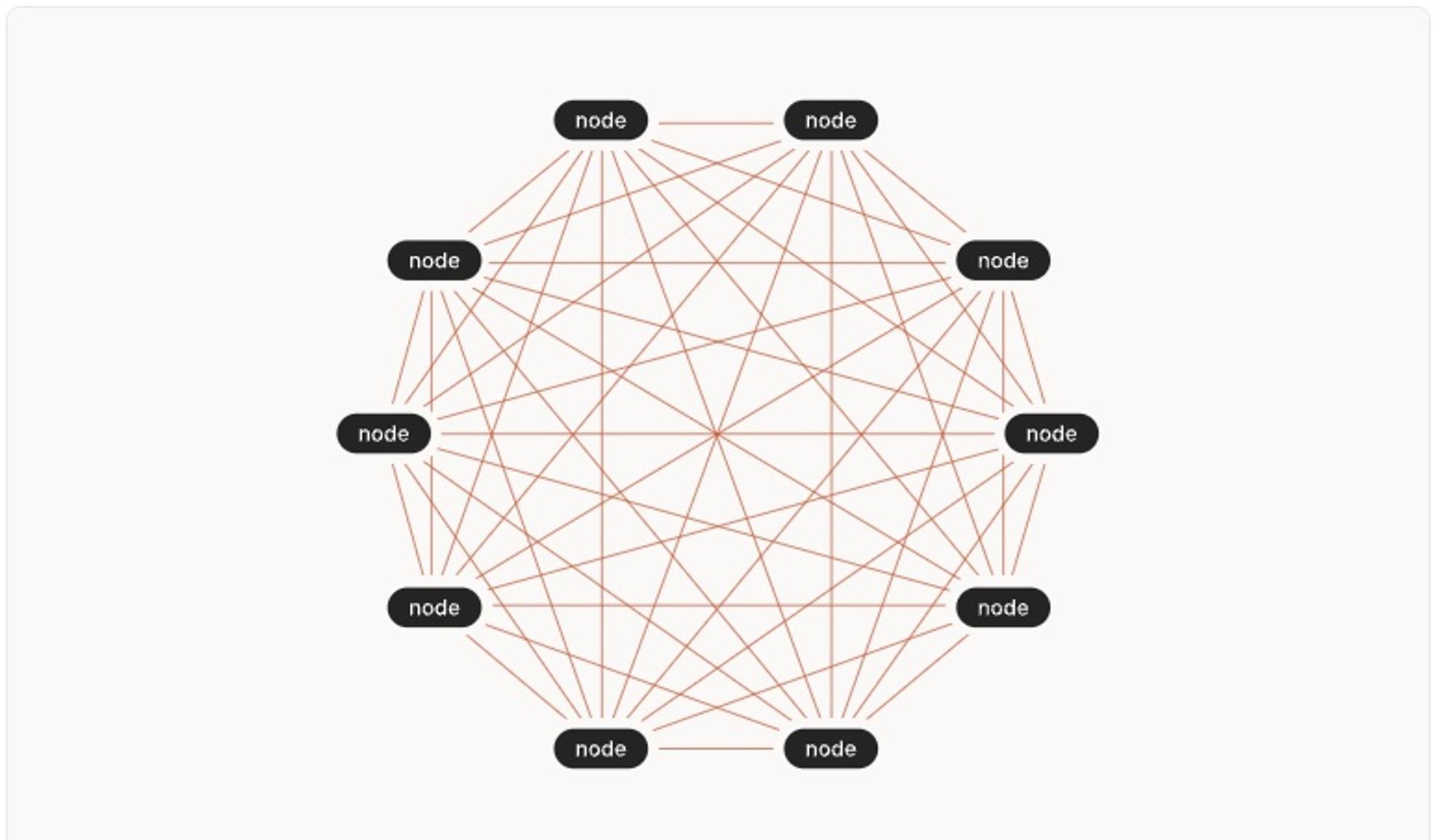
A mesh network is a type of networking topology in which different nodes dynamically connect to each other in order to improve the overall efficiency of data transmission.
What is a Mesh VPN?
Mesh VPNs use a peer-to-peer (P2P) model to create a secure shared environment for their users. They consist of nodes that send traffic between themselves rather than through a central server.
This is in contrast to the traditional hub-and-spoke model, which sends everything through a main server, creating a bottleneck. As nodes are added, scaling issues can limit performance.

In addition, users that are distant from the VPN gateway will experience sluggishness due to latency, even when the server is not busy. It also leaves the VPN gateway exposed, and authenticated users often have access to the whole network, which creates risk.
Without a central server, a mesh VPN network frees you from these issues, increasing security and scaling efficiently. You can add nodes without overloading the network, and connections use the shortest path available, which minimizes latency.
In this article, you’ll learn more about how these VPNs work, along with best practices for getting the most out of it. You’ll also learn what options you have if you’re thinking of using a one for your own network.
Mesh networking explained
In a mesh VPN, nodes do most of the work that would otherwise be done by a central managing server. In a regular VPN, all the data goes through this central server, whereas in a mesh private network, nodes send data to each other, spreading the burden throughout the system. In this section, we’ll cover some of the basics of how these VPNs work.
How nodes communicate in a mesh network
The nodes within a mesh network maintain lists of other nodes, which they connect to as needed. The pattern of connections between them forms a mesh which frequently changes as connect and disconnect to each other at any time. However, the fundamental architecture remains the same.
Nodes may drop, and in some systems the best routes through the system are dynamic, but the network is always a set of interconnected peers. Once connected, nodes may get information from other nodes, keeping each other updated as things change.
Configuring exit nodes in your Tailscale network
As mentioned, mesh VPNs rely on a P2P model. Some, like the open source project tinc, use the mesh to handle everything. However, this is unusual as most aren’t fully P2P: They use a central server of some kind for coordination. The coordination aspect is often called the control plane, whereas the secured traffic between nodes is often called the data plane.
Mesh VPN design
The nodes in the VPN can vary in nature. Wireless routers, phones, desktop computers, or servers can all act as nodes.
Although the mesh structure lends itself to better scaling than a hub-and-spoke configuration, there can be issues with scaling.
For example, individual mesh nodes may have less capacity than one large hub would. Each connection to another node has some overhead, and mesh VPNs that relay traffic between nodes (versus only making direct connections) can lead to network traffic and congestion on the relay nodes.
Mesh VPNs can also be challenging to manage. Figuring out the shortest routes around a network with relays is a complex problem, and the algorithm used by them is a key factor in the network’s overall performance. The VPNs that do not use relays have the problem of making direct connections between devices that may be behind NAT (which impedes direct connections as a side effect) and firewalls (which exist primarily to prevent unauthorized connections).
Mesh network features
Several distinctive features differentiate mesh networks from other types of VPNs.
The core feature is its distributed nature. Avoiding the use of a central server (aside from adding nodes) reduces latency and makes the network far more scalable. Other features are consequences of this architecture.
Shared internet access
Members of this type of VPN can share each other’s internet access. There may be one or several points connected to the internet, with requests sent through the system to reach them. Internet traffic is then routed back to the requesting node.
These VPN connections may not offer all the features you expect. They are typically used to secure communication between devices owned by an individual or organization, rather than for anonymizing internet traffic. In fact, all connected devices can usually identify your internal ID. It’s like having a local setup that isn’t physically wired together.
If the network uses a common resource to provide nodes with internet access, sites you connect to will see a common IP address and may be able to track it. So while information you exchange between nodes isn’t visible to the outside world, your internet connection or location aren’t necessarily masked as in a privacy VPN marketed to individuals for anonymizing their internet browsing.
Self-discovery and healing
Mesh VPN algorithms allow nodes to continually decide how to best pipe traffic through the system. These algorithms mean that the network can be self-discovering and self-configuring, and precise routes from node to node are determined dynamically.
The best mesh VPNs are also self-healing: The nodes are constantly figuring out the best route to send traffic, and if one of them goes down, they simply pick another route. That means you’re less vulnerable to outages and network issues.
Note that depending on a particular architecture, your control layer could be a possible point of failure, though existing nodes should be able to carry on without it. If the control layer fails, however, new nodes won’t be able to connect until it’s restored.
Better value
Another architectural benefit is that the nodes do much of the work of managing the network. This means less central processing and bandwidth is required.
With nodes moving data around, you don’t need to spend as much on your infrastructure. For VPN providers and customers, those services can provide better value.
For example, Tailscale is free for individual use despite including most of the features you’d want in a paid VPN. Besides secure connections and HTTPS, you get things like single sign-on and multifactor authentication (MFA), which builds on top of WireGuard®.
Mesh Networking Use cases
Direct peer-to-peer connections
Nodes connect directly to their peers. You can therefore create a remote network exclusively for a certain group of users, such as employees of your company. The VPN also allows you to connect employees in different departments or offices and give them a common set of internal services.
Faster access to common resources
For companies that want to connect multiple sites in different locations. People are connected via the VPN, and from a user’s perspective, everyone is working on the same network. The VPN achieves this without needing an intermediary to manage all its traffic.
Common resources can be shared without having to pipe all the traffic through a central location. This makes things faster and prevents bottlenecks. Traffic is free to take the fastest available route from A to B.
Experimenting with new services
Rolling out new features on a network can be risky. A new service is untested and vulnerable to attack. You may also be vulnerable if you’re making small changes to your system on a regular basis as you may not have had the time to put everything through a security audit.
The private nature of a VPN means you can test services without exposing them to the wider world, which minimizes the impact of mistakes. No one outside your community has access to the system. This means hackers are less likely to exploit weaknesses, and errors are unlikely to be spotted.
You can even create a local network just for your developers and use it for experimentation before adding new services to the main VPN.
Private networks are completely under your control and free from outside interference. The consequences of mistakes are limited, making them ideal for trying out new features.
Basics and configuration
In this section, we’ll suggest how to get started setting up and initializing your mesh network, explain how node connections work, and provide some key considerations around your firewalls and control plane.
Despite their advantages, mesh VPNs can be complicated. Each node needs to manage its own routing independently, and information on peers needs to be exchanged.
The choices you make when setting up a network will define its effectiveness. This is even more important as you scale up, because more nodes mean more complexity and longer routes to calculate.
Getting started with configuration
There are many existing solutions to help you get started. One simple solution is Tailscale, which handles configuration for you. It connects the nodes securely and creates a central control plane to coordinate everything. This saves you time: You can quickly start using the network without developer effort in setting it up. You won’t have to go back to fix errors, either.
Tailscale’s client is open source, so you can check out how everything works and change whatever you need to. The Tailscale coordination server is a closed source SaaS product but is free for personal use.
Initializing a Tailscale mesh VPN
When first connecting, the node contacts the coordination server and registers its public key. It also tells the server where it is — in other words, its IP address, which port number to use, and which relay server it can be reached through.
The node then downloads information about the other nodes in its domain. That way it knows the addresses and public keys of its peers. With this information, the node is now free to connect to other nodes without further reference to the central server.
The coordination server keeps all the required information on the various nodes, such as their IP addresses, for sharing with other nodes.
Node connections
Nodes use key pairs to connect securely. Each node generates a public and private key pair for itself. The public key is associated with its identity.
In public-key cryptography, the public key is shared and used to encrypt data that requires the private key to access. The private key always stays with the central node and is never shared.
This keeps everything secure as the public keys are useless without the private key. Both are needed to connect to other nodes securely.
Firewall management
Managing firewalls is a huge challenge, not least because some nodes may have limited control over the firewalls they need to go through. Opening firewall ports isn’t always possible for nodes connecting via networks where you do not have administrator access, including cafe or hotel Wi-Fi. Better options are needed.
Tailscale can also help in this regard because it uses advanced NAT traversal techniques. These essentially allow connections to avoid many of the restrictions a firewall creates. This means you can work over connections even when you can’t change those connections’ firewall settings.
Control plane features
Besides handling initial coordination, control planes let you set company-wide rules. You can decide things like which devices and users are allowed to access which resources, then upload those security policies in the control plane for all the nodes to download and follow. This way, you can make sure all the nodes on the network are enforcing the same security policies.
Security considerations
Now let’s look at some broader security considerations when setting up this type of VPN.
Encryption
Make sure the data you share is not readable by third parties. Tailscale, for example, uses the open source WireGuard protocol to create encrypted tunnels between computers on the network, making it unreadable to eavesdroppers.
There are several other things you can do to keep your network safe.
Use a zero trust approach
The default policy for good security is zero trust. That means you give minimum possible permissions to every node. Security checks are carried out every time a transaction is made. Specifically, when permissions need to be granted, an authorization check is carried out. Permissions are granted temporarily and revoked as soon as the transaction is finished.
"Zero Trust Networking" definition
MFA is a complementary practice to a zero trust approach. If credentials are lost or stolen, MFA provides another layer of protection to prevent unauthorized users from gaining access your network.
MFA typically involves sending a code to a device, but it can also use biometric data or physical tokens. By requiring the use of a specific device or other means of authentication, you prevent hackers from breaking into your system simply by stealing a password.
Implement role-based access control
When granting remote access to different resources, you need a system to decide who can do what. Developing policies to assign users permissions makes your network more secure.
Role-based access control, or RBAC, lets you assign permissions to nodes on the network depending on the associated user’s role. If permission is granted to the role, then all individuals who have that role get access automatically, saving considerable admin time. Managers can then decide what role to give team members when they’re first granted access to the network. Of course, team members’ roles can change if required.
The control plane can handle distribution of permissions during initialization. Using RBAC means you don’t have to assign users permissions individually and makes it easier to ensure everyone has the permissions they should have. RBAC also allows you to make changes that affect large numbers of users together. In a large organization, this makes it much easier to implement a business-wide decision regarding who can access any particular resource.
Conversely, if permissions are granted on a case-by-case basis, it’s easy to forget when someone should lose access to a resource. Over time, your system becomes less secure as users have permission to access resources long after they’ve changed roles. In a worst-case scenario, users can be left with permissions after they leave your company. That can be a vehicle for malicious attacks.
Change security settings as needed
Company security policies can also be stored on the central control plane. This is accessed by nodes when they enter the network. For example, some networks allow full access between nodes, while others are more restricted.
Having these policies stored in a central location makes them easy to change. Admins can and should update security policies to reflect the evolution of the network. Updates to software, emerging threats, or changing user profiles can all lead to making changes that better reflect your needs.
Secure key rotation
Nodes need to know each other’s IP address and encryption keys to exchange data. You need to exchange keys between them securely. Tailscale handles this by recording in the coordination server which encryption keys are in use and supplying those details to all of the nodes.
The architecture of this control plane for initializing nodes is the same as in the hub-and-spoke configuration, but the impact on performance is minimal because it’s only used briefly when nodes connect to their peers. After that, the traffic passing between the nodes is routed through the mesh.
How Tailscale can help with mesh networking
A mesh topology lets your nodes handle network traffic and avoids the need for an overburdened central server to manage everything. It’s performant, scalable, secure, and lets geographically distributed companies work together on a common network.
Deployment can be difficult. There are firewall issues to worry about, configuration challenges, and complex algorithms to pick from. Choosing a solution that can handle these issues lets you get started quickly without having to set up everything yourself. It means you get security and performance right from the start.
If implementation seems overwhelming, have a look at Tailscale. It’s simple and fast, and it requires no configuration. Chances are your devs already love it, and can have your enterprise up and running in no time.
Try Tailscale for free - no credit card required.
FAQs
What is a mesh VPN?
Mesh VPNs use a peer-to-peer model to create a secure shared environment for users via nodes that send traffic directly between themselves. By contrast, a traditional hub-and-spoke model VPN architecture sends everything through a main server, which creates a bottleneck.
What are the benefits of using a mesh VPN?
Compared to a traditional hub-and-spoke VPN, a mesh VPN scales efficiently, allows you to add nodes without overloading the network, and ensures connections use the shortest path available, which minimizes latency. Essentially, a mesh VPN spreads the work around, letting your nodes handle network traffic and avoiding the need for an overburdened central server to manage everything.
Are there drawbacks to using a mesh VPN?
Mesh VPNs are complicated and can be difficult to deploy. Each node needs to manage its own routing independently, and information about peer nodes needs to be exchanged. There are firewall issues to worry about, configuration challenges, and complex algorithms to pick from, but choosing a solution that can handle these issues lets you get started quickly without having to set up everything yourself.





