Bringing Tailscale to Work
Tailscale users generally try Tailscale at home for personal networking, remote access, and connectivity before solving those same issues at work. However, companies often need advanced integration, compliance, support, and access control at scale. Bringing Tailscale to work can be relatively simple and in this article we’ll explore how. We’ll also discuss the nuances of using Tailscale for any number of users and devices — from just a few to hundreds or thousands.
How to get started with Tailscale in the enterprise
Getting started with Tailscale at work is similar to getting started at home.
Just like at home, Tailscale works with existing identity providers (IdP) such as:
- Okta
- GitHub
- Microsoft
- Others
Tailscale also works with custom identity providers via custom OIDC
Here’s how to get started with Tailscale at work:
- Download Tailscale on the device you want to be added to your Tailscale network (tailnet). Tailscale runs on most operating systems, including Windows, Android, Linux, Mac, and iOS.
- Install Tailscale on the resources you want to be added to your tailnet. You can also use the Subnet router feature to quickly add lots of resources at scale (or if you aren’t able to install Tailscale).
- Edit your access control lists (ACLs) for users and devices.
- Use ACL tags when adding servers; by tagging a server, you can remove the human identity from it, which is beneficial if the person setting up the server leaves your organization.
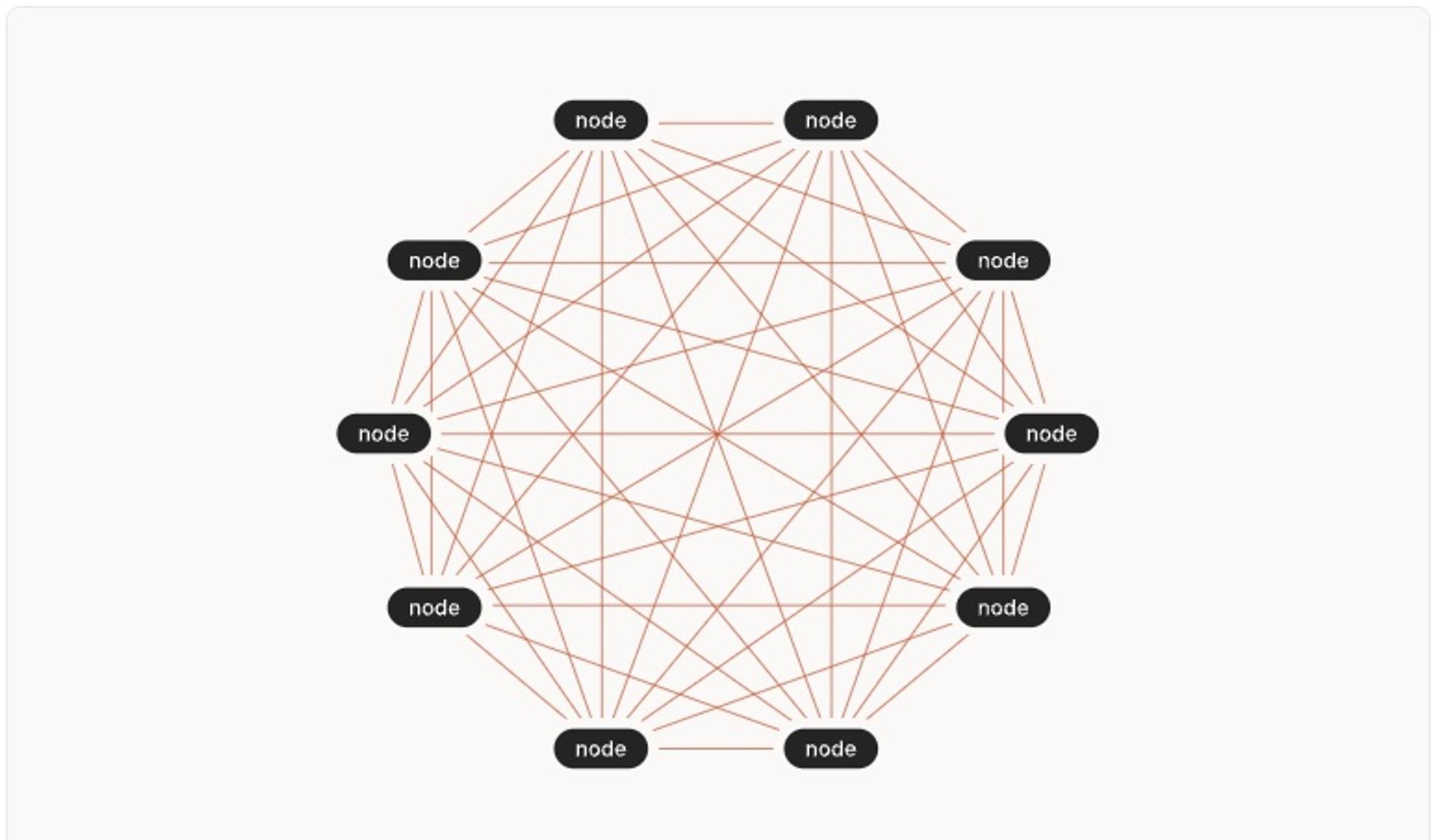
Comparing Traditional VPNs to Tailscale
Unlike traditional company VPNs, Tailscale is mesh-capable, which means that connections are peer-to-peer instead of being funneled through a centralized location. Let's compare the two starting with traditional VPNs.
Traditional VPN:

- Susceptible to lateral attacks
- Performance bottlenecks
- Limited SSO/MFA integrations
- Frequent reauthentication
- Extra hops (higher latency)
- IT support & maintenance
- Limited OS support
Tailscale's Solution:
- Device-level access control
- Fewer bottlenecks
- Auth and users governed by IdP
- Peer-to-peer connections
- Lower latency
- Keys & Certs management
- OS support: Android, iOS, MacOS, Windows, Linux
With Tailscale, you can share private company resources with your team, without exposing those resources to the public internet. For example, installing Tailscale on your API server allows your team to access the API server from anywhere. You can also label the API server, “API server” and access it by that name instead of its Tailscale IP.
Key features to know when bringing Tailscale to work
Tailscale works with nearly any tech stack, allowing teams to continue using their current tools and infrastructure. Here are other Tailscale features your enterprise can benefit from:
- Tailnet lock: Prevent new, and potentially malicious, nodes from joining your tailnet without first being signed by an already trusted node. When tailnet lock is enabled, even if Tailscale infrastructure is compromised, attackers won’t be able to add new devices to your tailnet.
- Custom OIDC: Tailscale can integrate with any identity provider that supports OpenID Connect (OIDC).
- User & group provisioning (SCIM) for Okta: Sync group membership and new or deactivated users from Okta.
- ACLs: Managing access is handled in the Tailscale ACL policy file. In this policy, admins can define what users, groups, and tags have access to in a scalable way.
- Tailscale works for both development and production environments: Teams need secure remote access to both development environments and production environments. Teams need access to resources such as databases, servers, devices, VMs, containers, internal applications, and more to effectively do their jobs. Operational functions such as IT and Security, need ways to manage who has access to these environments and infrastructures quickly and securely.
- Aligning IT and security team priorities: Tailscale combines connectivity and security and can help align IT and security team priorities. IT is in favor of connectivity (adding more users & devices), and security teams are in favor of security (limiting the number of users, devices, and what they have access to). Tailscale helps align these two teams because the easiest way to add a new user or device to a tailnet also happens to be an incredibly secure solution that brings identity, explicit access controls via ACLS, etc. Instead of both teams promoting their solution, they can both use Tailscale.
- Invite external contractors to your tailnet: For organizations using Tailscale, you can now invite anyone to your tailnet even if they’re on a different domain or using a shared domain like Gmail. For example, external contractors, partners, freelancers, vendors, etc, can all be invited to your tailnet without setting up a temporary email account or adding them to your IdP.
When you add an external user to your tailnet, your existing security controls, ACLs, and user approval settings will still work to keep your network safe. Admins can limit whether your users can join external tailnets in case you do not want your users accidentally accepting an invitation to join a competitor’s tailnet.
By default, only Admins can join external tailnets, but you can disable anyone from joining using the “Join external tailnets” option in the Feature Previews in the admin console. You can also monitor when invitations are created and when users join a tailnet in the audit log.
Teams can use Tailscale - regardless of device location or environment - with the tech stack they are already on.
Key Security Features of Tailscale
Tailscale connections are end-to-end encrypted with WireGuard®. WireGuard is a modern VPN designed for usability, performance, and security. WireGuard uses state-of-the-art cryptography and provides end-to-end encryption for connection between devices. WireGuard’s protocol has been reviewed by cryptographers and the code audited, with only minor issues discovered and fixed.
These are six key security features of Tailscale:
- SSO and MFA: Tailscale relies on your existing identity provider to authenticate users, and automatically uses authentication settings like MFA.
- Access Controls Lists: ACLs allow you to define which users can connect to which devices in your network.
- End-to-end encrypted: Tailscale is built on top of WireGuard, a modern VPN that provides end-to-end encryption between devices. Tailscale sees your metadata, not your data.
- SOC 2: Tailscale has implemented procedures and policies in line with AICPA’s trust services criteria.
- Latacora Audits: Tailscale works with Latacora, a security firm that specializes in information security, to conduct security audits.
- Security Bulletins: Tailscale publishes security bulletins to disclose security issues in our product.
For a deeper understanding, please visit this Security at Tailscale page on our website.
Ready to bring Tailscale to work?
If you are a home user of Tailscale and are curious to see how Tailscale simplifies networking and brings peace-of-mind for teams of every size, check out our customer stories.
The Tailscale free plan is a great way to get started as it includes every feature and takes just a few minutes to get set up: try it now.
When companies are ready to roll out and scale with advanced integrations, compliance, and support for access control, head over to our pricing page for pricing information on Tailscale.
Related resource: [Contact us] Get started with Tailscale for your team






