Tailscale SSH Console
SSH from your browser to devices on your Tailscale network

SSH from any browser
Initiate a secure browser-based SSH session from any device - even if you aren't running Tailscale on that device!

Work anywhere

Quick to start

No install required

Automatically terminate sessions
SSH access in an emergency
Respond to an emergency with whatever device is on hand: authenticate to Tailscale from any browser to SSH into devices on your tailnet, without installing a local client.

SSO & MFA
Use your existing identity provider and multi-factor authentication to protect SSH connections. Protect SSH connections the same way you authorize and protect application access.
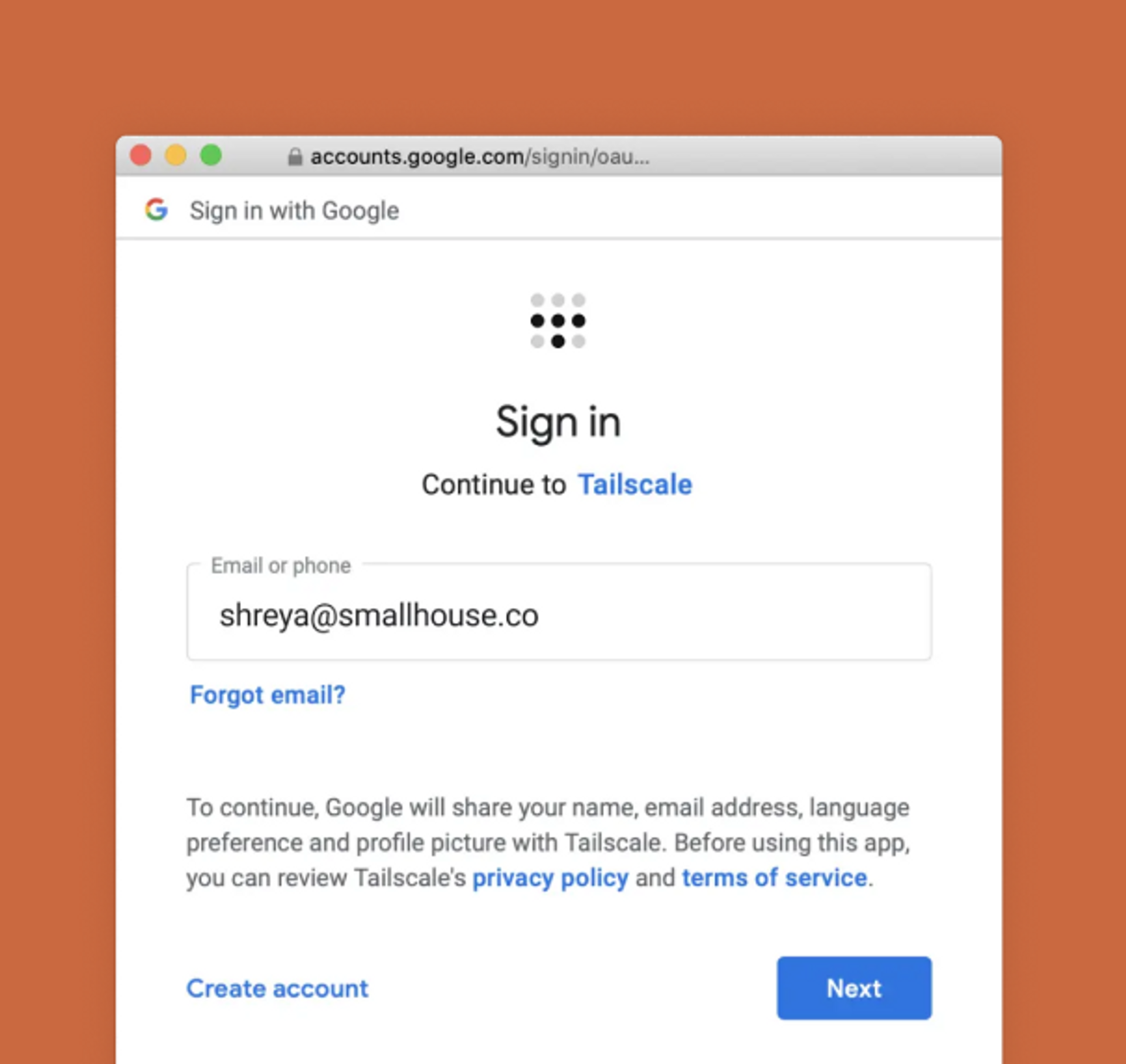
Re-authenticate SSH connections
Re-authenticate users before establishing a Tailscale SSH Console session, using your identity provider.
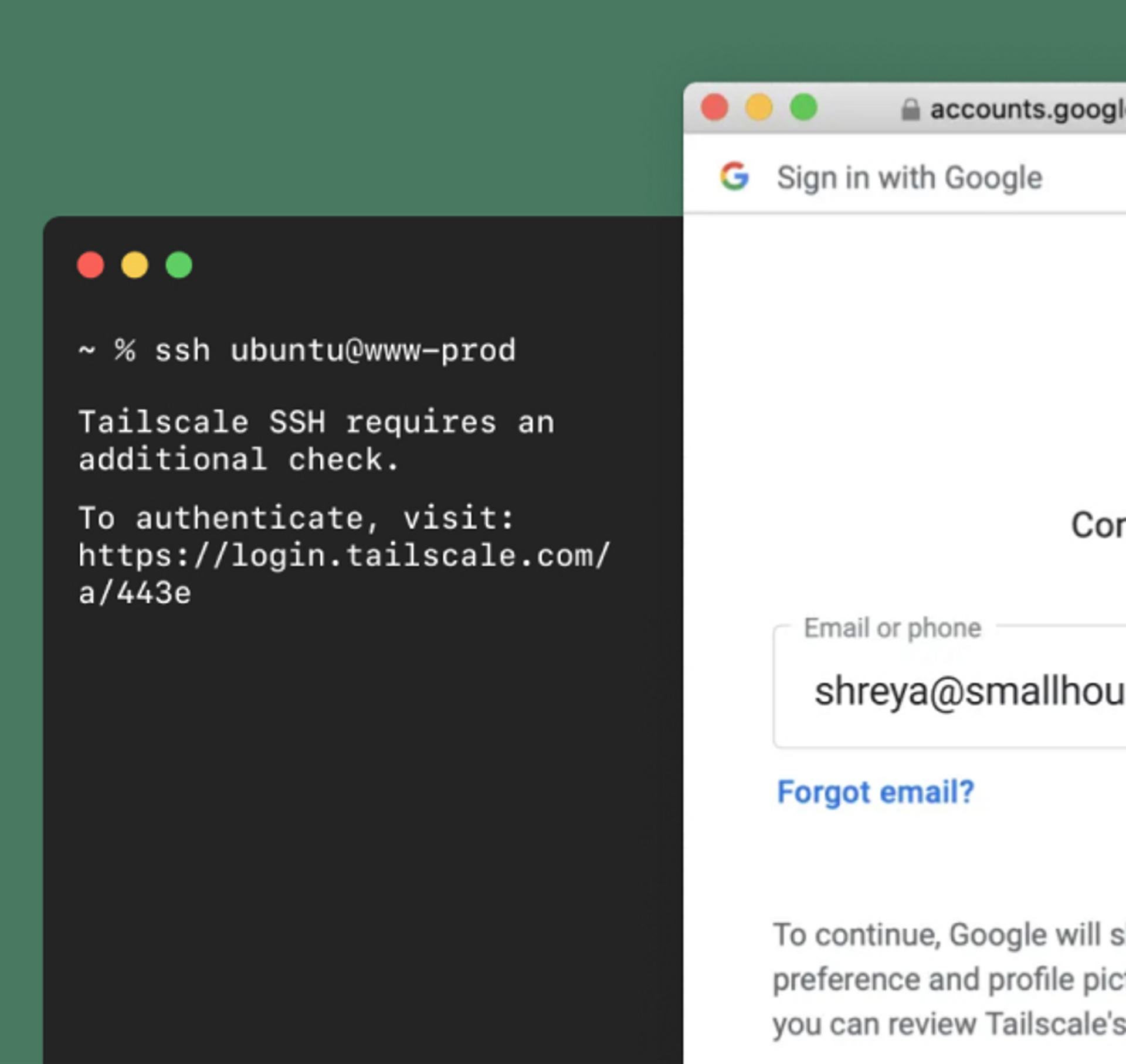
Tailscale SSH Console runs in your browser
When you start a session, an ephemeral node is created in your browser using WebAssembly, which stores keys in memory only. Sessions automatically terminate when you close the browser window. Your connection is end-to-end encrypted.

Authentication & encryption
Authenticate, authorize and encrypt SSH connections using Tailscale. Rely on Tailscale to manage access for SSHing to machines on your network, instead of managing SSH keys. Tailscale can't see your traffic - it's end-to-end encrypted.

Manage permissions as code
Define what connections to your devices you want to allow using a standard syntax. Understand your SSH access controls in a centralized configuration file.







