Sometimes a great Tailscale use case arrives fully formed, simply asking to be documented. Like Bambuddy, a self-hosted tool for controlling Bambu Lab 3D printers locally, that all but walked up to my desk this week.
Bambuddy has gained attention as 3D printer maker Bambu Lab makes yet another move that the company frames as security, but a vocal community sees as tighter controls. Bambuddy offers another path: it replaces what Bambu's cloud does locally, and its Tailscale integration provides remote access without opening ports or using another cloud.
“Bambuddy doesn't use Tailscale because it's a cool integration,” developer Martin Ziegler wrote me in an email. “Bambuddy uses Tailscale because it's the only way to give self-hosted users the remote-access ergonomics they're used to from cloud-printing without putting them back on a vendor cloud.”
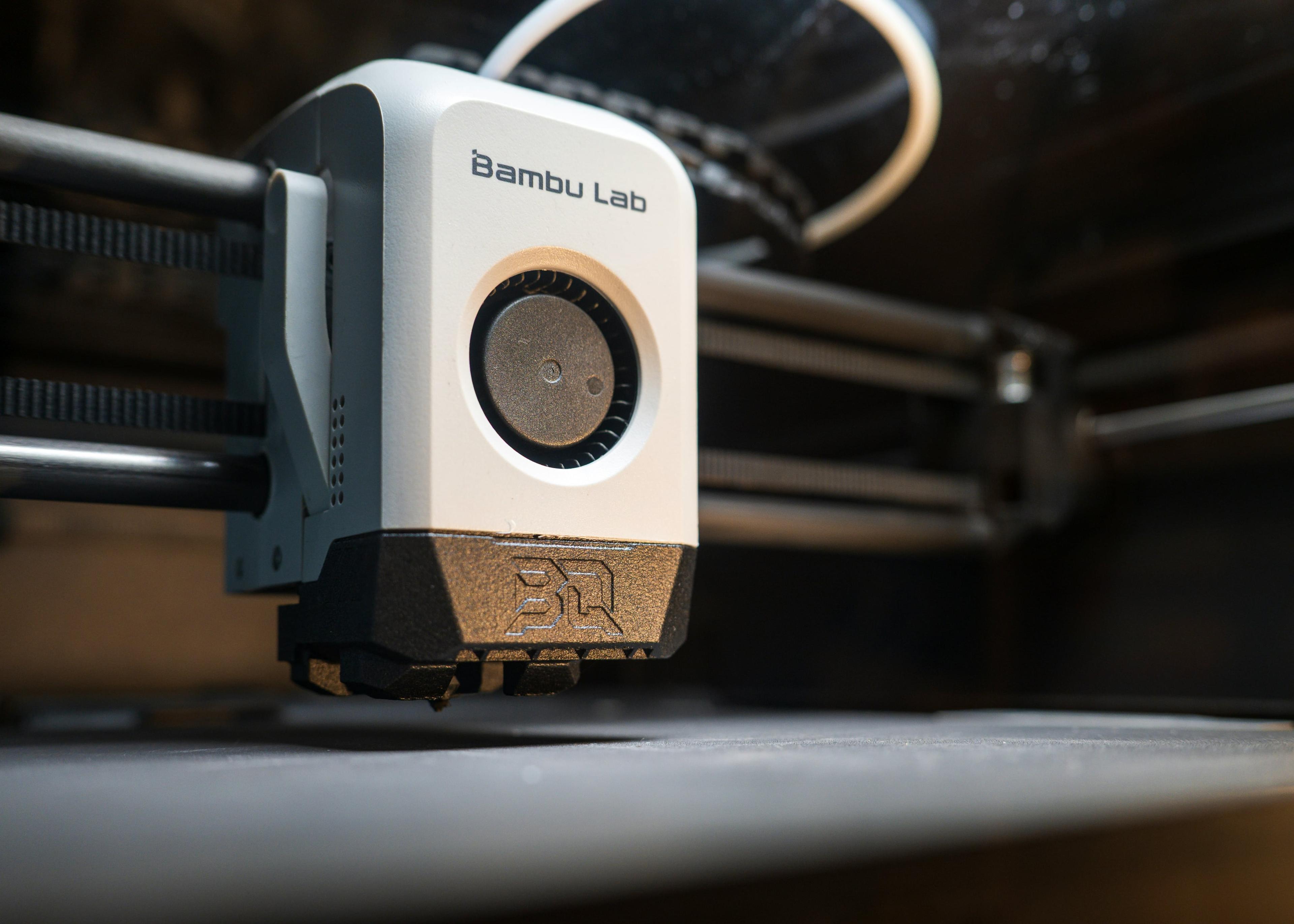
Top photo by Productivity Garden on Unsplash.
Bambu Lab gets legs, gets defensive
Bambu Lab launched its first products in 2022 and quickly gained traction in the 3D printing market. Its models did two key things: print faster than other models, and remove the need for many frustrating adjustments and maintenance tasks. Part of Bambu’s “just works” appeal was its cloud service, which allowed sending and monitoring prints remotely.
Bambu fans started building their own tools to augment or supplant Bambu’s software, like OrcaSlicer, an alternative tool for converting designs into print-friendly “slices.” OrcaSlicer was forked from Bambu’s own AGPL-licensed Bambu Studio (itself forked from PrusaSlicer, in turn forked from Slic3r). You could use OrcaSlicer, DIY screens, and other accessories with your Bambu printer, right up until Bambu described them as a security issue.
In early 2025, Bambu published a blog post with the not-exactly-friendly title “Firmware Update Introducing New Authorization Control System.” The gist was that Bambu’s printers would get firmware updates “to ensure only authorized access and operations are permitted.” Bambu pointed to high volumes of “abnormal traffic” in cutting off direct access for tools like OrcaSlicer. A new middleware layer, Bambu Connect, was offered as an authorized interface.
The backlash was immediate and effective. YouTube creators like Jeff Geerling and Louis Rossman spoke to concerns about customer rights and hardware access, along with some notably broad language in Bambu’s Terms of Use.
In response to questions from The Verge, Bambu said it would not require a subscription for any existing printer control function over a home network. It also said current models would remain “remotely controllable over LAN without user account or Internet access.” (I wrote about the events and blowback at that time for Ars Technica).
Virtual printers for real control
Bambu, having tried to set terms with its creative community, instead inspired that community to creatively work around them.
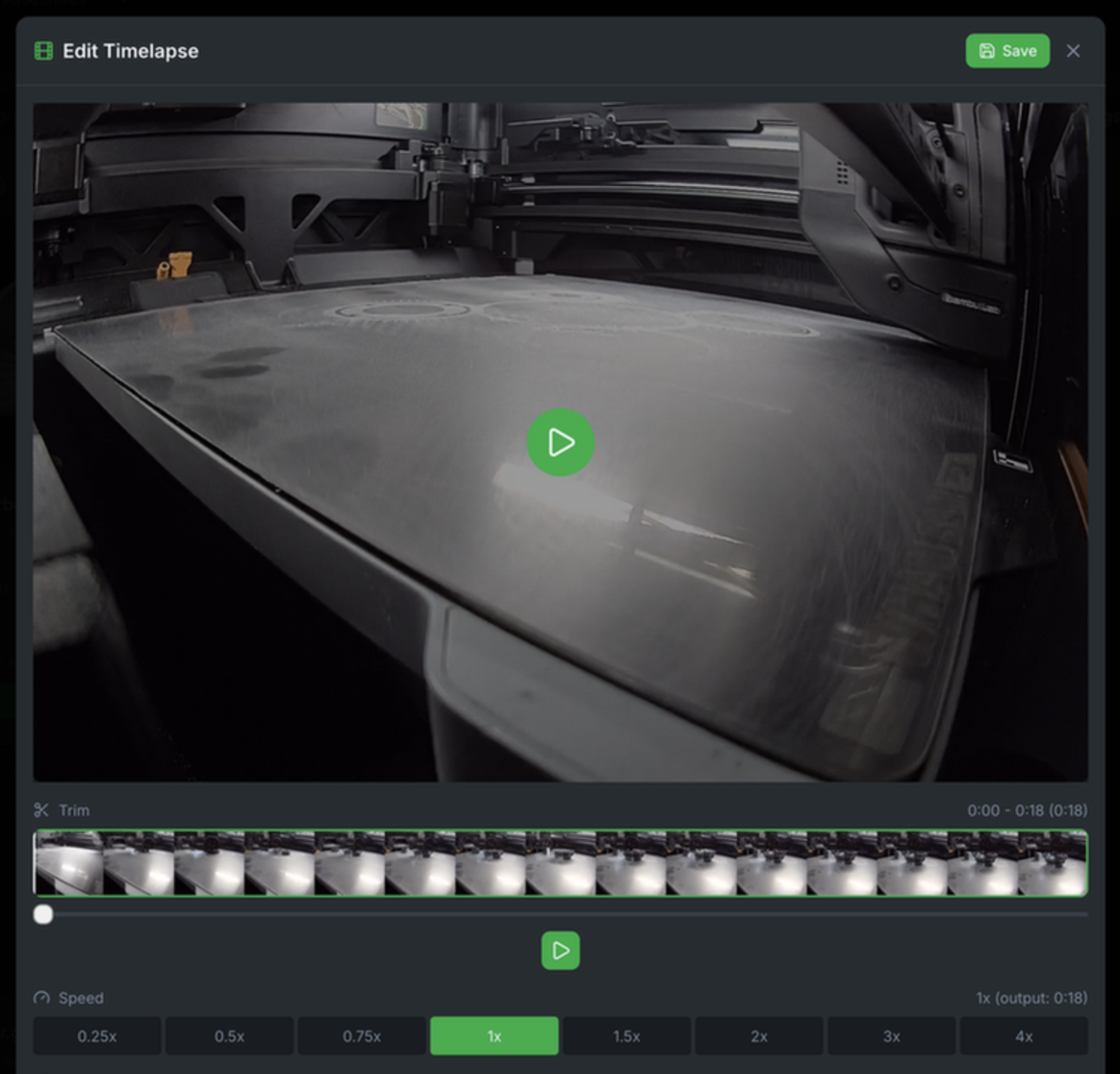
In late 2025, Bambuddy, an open-source, self-hosted app aiming to replace most of Bambu’s cloud offerings, came online. Using Bambuddy requires putting a printer in “LAN Developer Mode,” which disables Bambu’s cloud and the Bambu Handy app and model library. In early 2026, Bambuddy added a virtual printer and proxy system, so that apps like OrcaSlicer can discover and send prints to a printer in LAN Developer Mode.
Ziegler, the developer, told us Tailscale was the next logical step to providing a no-cloud-needed setup.
“That [virtual proxy] model is great until you leave the house. The user request that kept coming up was: ‘How do I print to my Bambuddy from my laptop at work without exposing anything to the public internet?’ Tailscale is the obvious answer—private tunnel, no port forwarding, no DDNS, no trusting another cloud just to escape Bambu's. It slotted into the local-first design without compromising it.”

Are user agents “reverse engineering”?
Developer Pawel Jarczak went a different route to avoid compromise. His OrcaSlicer-BambuLab, a fork of OrcaSlicer, aimed to restore a direct connection between OrcaSlicer and Bambu’s printer controls—no Bambu Connect middleware, but also no need to activate LAN Developer Mode. This fork, according to Jarczak, used publicly available code from the AGPL-licensed Bambu Studio, along with his own integration work, to make the connection.
Bambu Lab contacted Jarczak, stating that a cease and desist letter had been prepared, and demanding that he take down his project. After the repository was taken down, Bambu Lab responded on May 7, 2026, with a blog post outlining their reasoning. Describing Jarczak’s tool as “injecting falsified metadata into network communication,” it cited a familiar concern: potentially overwhelming “unofficial” server traffic.
According to a note posted soon after by Jarczak, Bambu Lab’s accusations of “reverse engineering” and “falsified metadata” were centered on his tool setting a user agent to the name “BambuStudio” and a relevant version number. That user agent, Jarczak wrote, is present in Bambu Studio’s public source code, as well as the Linux client for Bambu Studio.
Murky clouds ahead
Two days after Bambu’s post, right-to-repair advocate and YouTube creator Louis Rossman lambasted Bambu Lab, and offered Jarczak $10,000 toward legal defense if he kept his code up. As I was writing this, Rossman posted another video, with the title “Bambu Lab: I'm reposting your code & I dare you to sue me.”
Jeff Geerling on YouTube described the situation as Bambu Lab threatening Jarczak “for things that developer didn’t do, using their own open source code,” and “blaming an individual open source developer for their own infrastructure and security problems.”
Back to Bambuddy
The dispute and dialogue drove new attention to Bambuddy. News coverage by Igor’s Lab, How-To Geek, XDA and other sites gained attention over the past few months. But there’s just something about cease and desist threats that motivates people to star a repository, and rethink whether they want more control over their printers.
Bambuddy allows for greater OrcaSlicer access to Bambu Lab printers and removes a cloud connection, while also offering remote access through Tailscale. Bambuddy integrates Tailscale through roughly 200 lines of Python code, in this manner:
- Tailscale is installed alongside Bambuddy, either on the host or in the same container
- Bambuddy uses a shell command to obtain the Tailscale hostname and IP address
- Each Bambuddy virtual printer can expose its Tailscale hostname or IP address
- OrcaSlicer or other tools can use that Tailscale IP address and reach Bambuddy over an encrypted connection—MQTT, FTPS, RTSPS, everything.
Bambuddy originally had a greater scope, intending to use tsnet to give each virtual printer its own Tailscale device, complete with signed certificates for each device hostname. For that to work, Bambu Studio and OrcaSlicer would need to accept each virtual printer’s Tailscale hostname and certificate. Today, they don’t: their “Add Printer” dialogs only accept IP addresses, and they trust Bambu’s bundled certificate authority rather than checking certificates against the system trust store.
If these were fixed, that idea might get revisited, Ziegler wrote, but for now, there’s a trusted connection that works.
“The integration is small because it doesn't have to be more—Tailscale does its job (private mesh, encrypted, no public exposure) and Bambuddy does its job (run the printer protocols locally),” Ziegler wrote.
It’s a straightforward story of two useful tools working together, even if the telling is a bit more complicated.
Have you integrated Tailscale into your 3D-printing setup? What changed, what’s better, and what’s still missing? Tell us about it on Reddit, Discord, Bluesky, Mastodon, X, or LinkedIn.

 Kevin Purdy
Kevin Purdy




