Zego provides vehicle insurance for gig economy workers in the UK. In the UK, a special kind of insurance is needed to make deliveries with a personal vehicle, which is normally paid by the worker upfront for a year. If you work in the gig economy part time, you don’t know whether you’ll make any of that money back for the course of the year. Zego solves that problem by letting gig workers pay for insurance incrementally instead.
Zego has grown quickly over the last few years, with its employee headcount now reaching 600+ people. However, this rapid growth has made it hard for their IT infrastructure to keep up with the changes in their team.
Before the pandemic, Zego supported remote workers with OpenVPN, which had reliability issues and a complicated setup, and was only intended for use by a small fraction of their workforce. When the COVID-19 pandemic broke out, the entire company moved to remote work. Debugging OpenVPN issues became more common and even more difficult. It was hard to tell whether a connection problem was a client issue, a DNS issue, or an implementation issue.
Zego Built a Custom VPN First
When OpenVPN didn’t scale, Cary Vidal (Director of Security and IT) and Bart Swedrowski (Director of Systems Engineering), looked for a solution. Their first approach was to create a home-brewed VPN based on WireGuard®, the same protocol Tailscale is built on.
WireGuard’s speed and simple setup made it quick to get started. However, after adding in authentication layers for two-factor authentication (2FA), a user portal to help ease configuration, a firewall configuration layer and a certification generation system, it became clear that this custom solution would take too much time to maintain. Cary and Bart’s efforts were better spent on growing the company in other ways. They didn’t want to become a VPN company!
Evaluating Tailscale
Cary and Bart had followed Tailscale’s development for some time, and reached out to see if it would be a good fit. “We’ve got some questions and our own VPN setup, but Tailscale looks really promising to us, because it’s got the client that we essentially want to build."
One question on the call was about how Tailscale only encrypts and routes internal traffic by default, rather than all traffic. While it’s common assumption that VPNs need to route all traffic for regulatory purposes, only encrypting internal traffic is fine for most kinds of compliance. Sending only necessary traffic through the VPN provides better performance for end users, but it also greatly reduces troubleshooting for Cary and his team administering the network.
After discussing security, performance, and pricing, Zego decided to move forward with Tailscale. It’s now a daily driver tool for their whole team.
Using Tailscale
Zego’s systems engineering team are the primary administrators of their Tailscale network. Using AWS and Tailscale, they’ve built a hosting platform that other Zego engineers use to build, deploy and run applications on top of CI/CD pipelines.
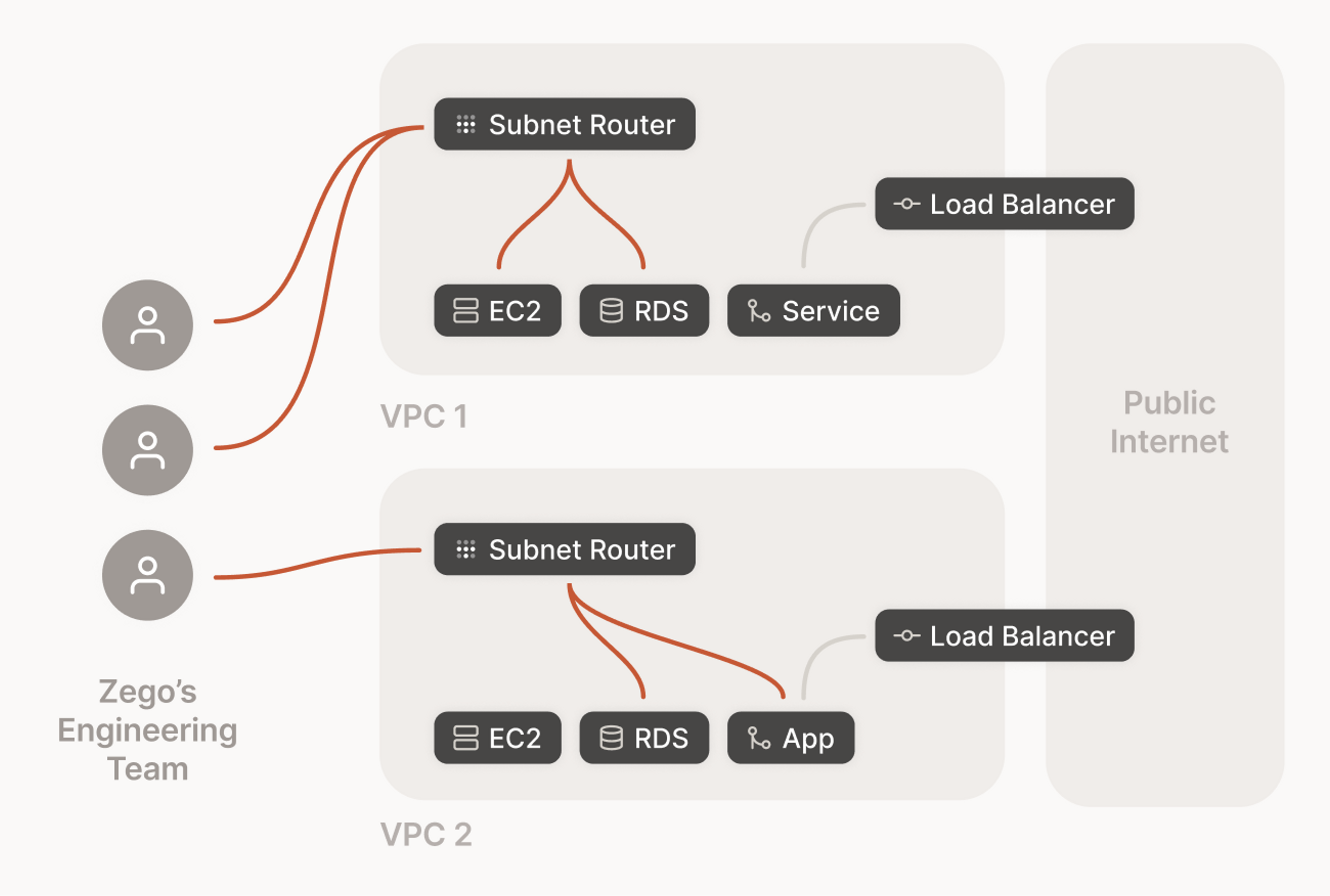
Tailscale provides secure access to this hosting platform. All of the infrastructure sits on private AWS VPCs in multiple regions, exposed over Tailscale using subnet routers. Connecting to this cluster of services managed by Kubernetes requires that users are logged in to Tailscale using their SSO provider and 2FA and authorized to access it.
“Trying to set up a traditional VPN resulted in our team spending a lot of time with support … we wanted a hassle-free VPN that will always be on while protecting our services, and is transparent to the end user. Buying Tailscale and getting that 25th iteration level of product completion on day one was a better deal for everyone.”
Tailscale doesn’t just help with remote access to production infrastructure, but also with local collaboration. The mesh network nature of Tailscale means instead of a front end developer and a back end developer running separate copies of the same stack, Zego engineers can collaborate on the same running codebase. One engineer can host the backend and another can connect directly to their machine with their frontend machine through Tailscale. Cary said “We could break down individual portions to help people work directly with each other. It’s like being in the same office.”






