Jasper trusts Tailscale to simplify, secure, and manage access

Tailscale performs 90% faster than Perimeter81, at 40% the cost
Jasper is a quickly growing company that buys multi-million dollar properties and makes the opportunity for investment in those assets available to users of their digital platform. Jasper is growing so fast, they grew their assets by over 10x in the last 6 months. As their engineers keep up with this growth and push the product roadmap of their platform forward, they can’t afford to compromise on security or developer efficiency. Oliver Shaw, CTO, and team were previously running a standard corporate VPN with some security concerns: the VPN connection represented a single point of failure, requests could be intercepted, and the dynamic IP addresses they relied on for IP allow lists could be reassigned at any time.
As Jasper grew, they needed a simpler way to authenticate access to their AWS environment. In addition to a large cloud footprint, including for code hosting, they run a private Sourcegraph instance that all of their engineers can access. Jasper reports that the initial set up process for Sourcegraph with Tailscale and MagicDNS only took 10 minutes.
Keeping up with Fast Growth While Pushing the Product Roadmap
Jasper used a corporate proxy-based VPN that gave users on its network a dedicated IP address. The traditional VPN was slow, had unreliable uptime, and also had security concerns: the connection represented a single point of failure, requests could be intercepted if the VPN company were attacked, and the IP addresses they relied on could be reassigned to another customer.
Jasper predominantly runs EC2 instances and Fargate containers in AWS and they needed a simple way to authenticate access to their AWS environment. In addition to a large cloud footprint for code hosting, they run a private Sourcegraph instance that all of their engineers can access. They wanted to make this available over a secure connection to search their codebases from anywhere.
Tailscale is Critical for Security at Jasper
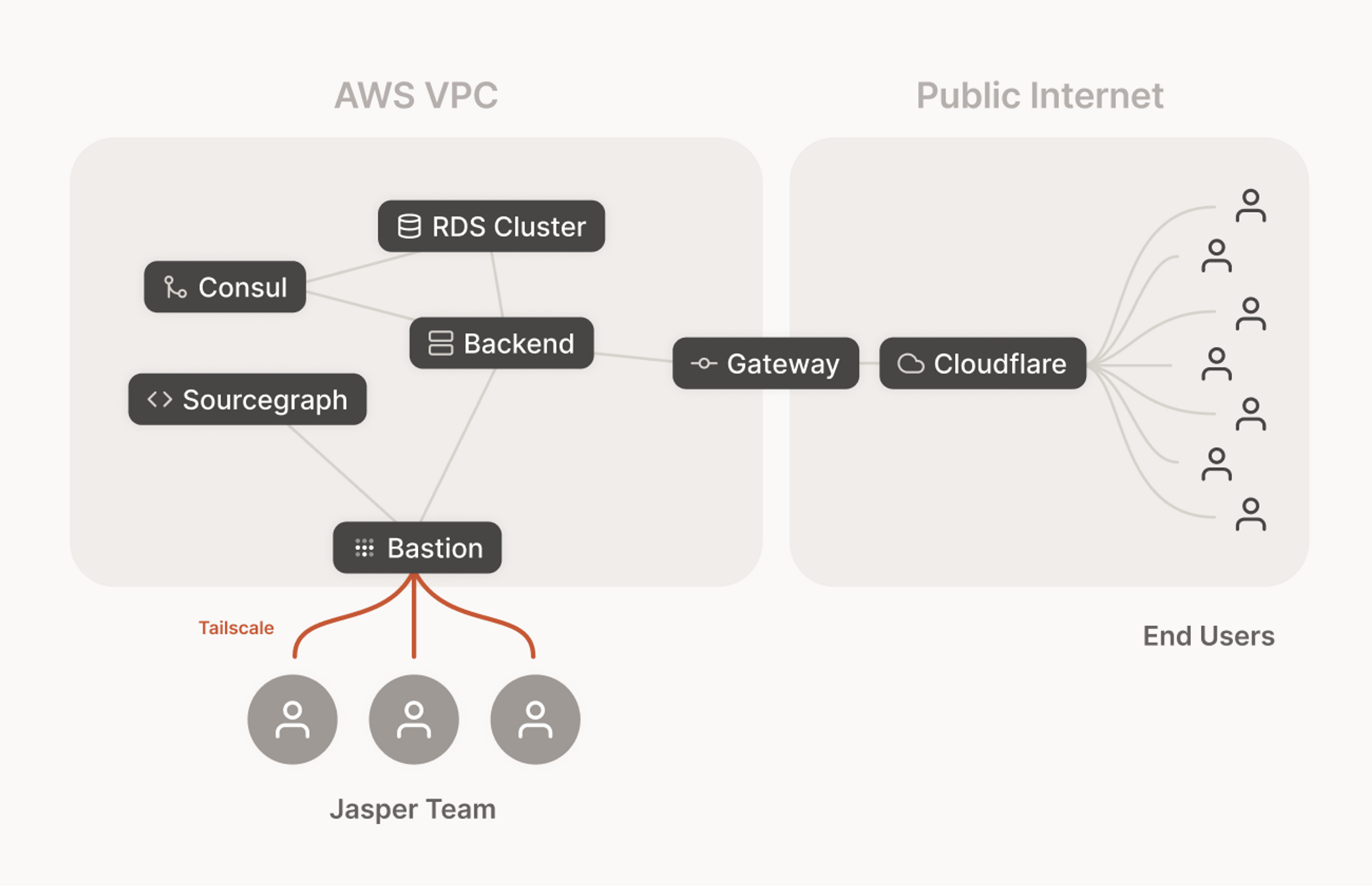
Jasper set up a single Tailscale account that is responsible for authenticating machines within their AWS environments. They have Tailscale machines set up for bastion instances in each of their AWS environments, sitting within a private subnet that is unreachable from the public internet.
Using Tailscale, Jasper engineers can securely ssh through to these bastion instances and remotely debug private AWS resources such as their containerized back-end services, RDS database clusters, and EC2 instances that sit in a private subnet that is inaccessible to the public internet.
To set up Sourcegraph, they spun up an EC2 instance that starts Tailscale and Sourcegraph. This works seamlessly as Tailscale establishes and connects through an encrypted network. According to Jasper, the initial set up process for Sourcegraph with Tailscale only took 10 minutes.
Jasper found that their latency when connecting to secure resources was reduced by more than 90% compared to their previous corporate VPN, thanks to more direct routing, and downloading database dumps is recognizably faster and less frustrating. “This really is the key: besides the latency, it’s easily getting up and running for your most complex servers, databases, and internal tooling” says Oliver. Furthermore, Tailscale costs less than 40% of their corporate VPN cost, and this gap will widen as they grow.
Oliver says that Tailscale is one of the most revolutionary tools he’s seen, and it has changed the way his engineering team works.
“As the CTO, I can quickly set up new instances of software like Sourcegraph that can be accessed securely by our team. Our engineers can also quickly and securely connect to our Consul nodes running in our secure AWS VPC for debugging, which was a major pain point. We’re immeasurably faster and so much happier.”





